
I don’t need to bang the drum about why security is interesting from a VC perspective. The constantly changing nature of attackers, tactics, techniques and processes, as well as a constant inflow of new controls and defence technologies, has made it a great space for venture investing.
Few sectors promise such consistent and high returns , especially as many more breaches are being detected every year. So much so that 2014 is now known as ‘the year of the data breach’. 2015 has starting off similarly, with a breach at Anthem that affected nearly 80m records. We can only expect the appetite for new protections to increase.
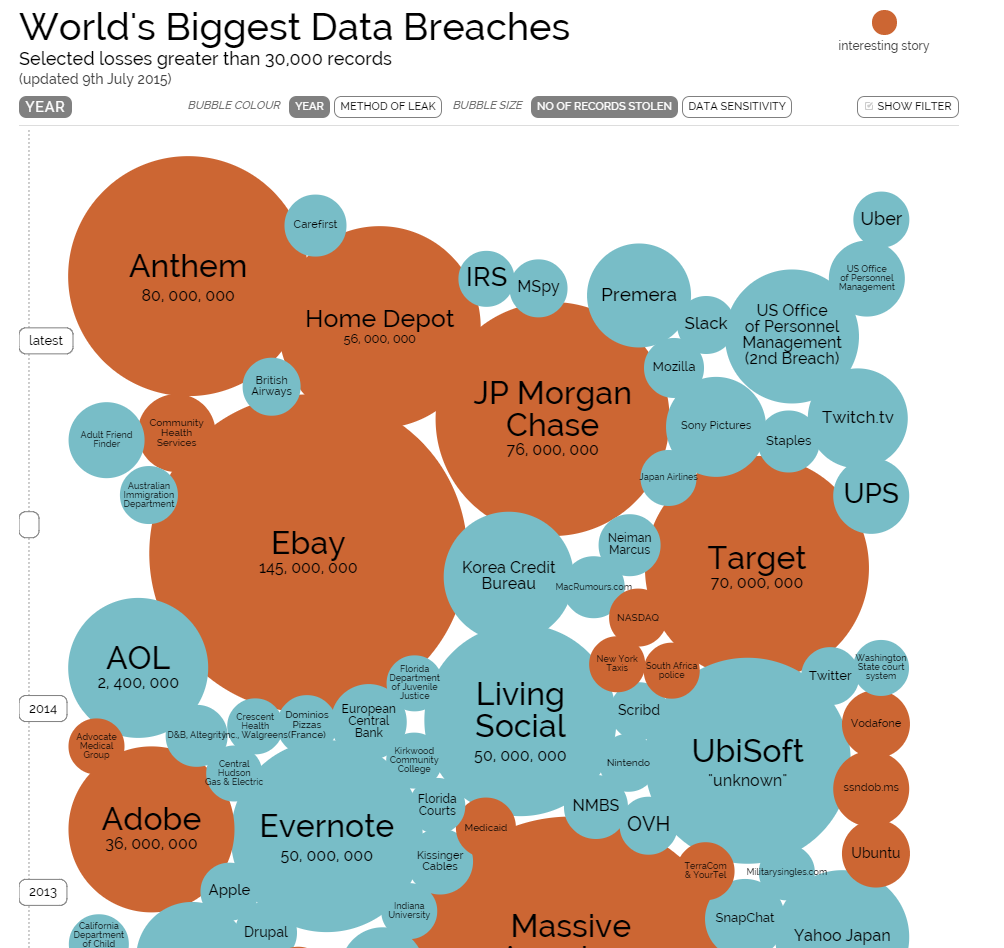
World’s Biggest Data Breaches (Source: Information Is Beautiful, DataBreaches.net,IdTheftCentre, press reports)
More scares around breaches, of course, mean more budget for security, and support is coming from the corner office — JP. Morgan’s CEO announced the bank would be doubling the spend limit on security in 2015 after breaches compromised data associated with 83m accounts and, in a great show of one-upmanship, the CEO at Bank of America suggested there would be no limit at all.
With all trends in the security industry pointing up and to the right, so is VC investing. But the game here is different, for both start-ups and the VCs who invest in them. When it comes to industry dynamics, customer behaviour, and the nature of product development, the logic seems to be flipped on its head: success in the industry depends on minimising the bad rather than providing a good, customers hide their pain points rather than talk about their needs, and a flawless product that is slow to market beats an MVP every time.
Over the past few months, as I have spent time with the teams at CyLon, London’s cyber security accelerator, I more often found the discussion moving closer to mental frameworks I built up as a consultant working with (slower moving) Fortune 500 companies than those I’ve formed through working with start-ups, i.e. building product through testing and scaling aggressively (and sometimes scrappily). It seems the usual start-up rules simply don’t apply here, and no one would dare utter the words ‘Lean Methodology’.
So what is different…?
The Customers
A few weeks back, I was hanging out in my lovely home town Malmö in southern Sweden, listening to Hampus Jakobsson of Brisk.io discussing the importance of Deer Hunting for SaaS start-ups at the Nordic Next conference. For those less familiar with the concept, the logic (laid out by Mark Suster in a post in 2009) is that start-ups in the SaaS space should avoid hunting elephants (the large, blue chip enterprise customers where there is a small chance of landing large $100K+ contracts), avoid hunting for rabbits (smaller contracts that seem like they’re in abundance but quickly turn out to be less valuable than the effort required to catch them), and instead focus on deer hunting. Deer are the customers that are large enough to be valuable but not so large they have ridiculous and impossible demands.
I generally agree with this logic. My advice to start-ups has often been to avoid chasing clients and contracts for which you risk dying trying to cross the desert — the desert in this case being the 18 month+ sales cycle. This generally includes any organisation in financial services, government and telecom. Unfortunately for security start-ups, these are the exact clients you want and need.
Although targeting SMEs may be the largest opportunity for security companies in the long run, the market is currently very different. Smaller companies either have fewer breaches or are simply worse at detecting them. Seen from another angle, cyber crime is, at its core an ROI-driven business — adversaries will be attracted to the most valuable data and the closer you are to financial information, the closer you are to financial return (all else constant). Either way you view it, demand for security products is concentrated with the large enterprise. On top of this, security is an industry where catching an elephant attracts more elephants, and potentially a long tail of deer in the long run. Signing customers that are known to be the gold standard in security, e.g. Goldman in financial services, gives the credibility to win more contracts.
Product Development
Eric Reis’ Lean Methodology has become the standard playbook for developing products and scaling businesses, where the best way to create a product that people love is to release one they love less, collect data and tweak the product until they love it more. There are a lot of areas where this is incredibly effective, especially for consumer products and increasingly for B2B products as the enterprise becomes more consumer-driven.
Unfortunately, the idea of an MVP doesn’t quite hold up in security, or at least the definition of ‘viable’ is totally different. Look at it from a bank’s point of view: if their data is 99% secure… it’s not secure. It’s not an industry where you can send a beta version out to market to test, and look to improve the solution in version two.
Secondly, it is not an industry where feedback is happily given. Unless you are in the inner circle, you are not going to get a lot out of a CISO you want to build a solution for. Outside of highly restricted industry associations and roundtables, actual issues and pain points are kept to secret.
This actually poses a huge challenge for security in general, as today there is no trusted place where information is shared on a larger scale. Anyone who cracks this will contribute hugely to the state of the industry (and national security). Investment in defence is far above that spent by cyber criminals, but while those defending keep their cards close to their chest, even from one another, those attacking most certainly share and exchange information.
The Entrepreneurs
Here’s where I’m undecided. As cyber-security companies ‘need’ to work with established organisations such as banks, telcos and governments; does this mean that typical young, energetic, slightly naïve, outsider entrepreneur not hold up? Does the idea of disrupting an industry with a new perspective simply not ring true when it comes to security?
On one side, entrepreneurs coming out of organisations like GCHQ or BAE Systems Detica will have access to information about the real issues CISOs are facing. They will also have a better understanding of controls already in use for specific clients and organisations that are more advanced when it comes to security. A lot of innovation is likely to come from commercialising solutions use in national defence and high-security organisations. The industry is also one where network is important to sell, as CISOs are prone to pay attention to tools recommended by people they know and trust. Breaking through the clutter is incredibly difficult in an industry where everyone claims to be selling a Lamborghini but few people know what a Lamborghini looks like. A number of early stage companies in the UK, e.g. Digital Shadows, Garrison Technology and RipJar, have significant security DNA.
But there is also merit in approaching this area from an outsider point of view and there are many stories of applying powerful technologies already in use elsewhere to the security space. Balderton portfolio company Recorded Future, for example, provides real-time threat intelligence through analysing open web data, and recently discovered login credentials associated with 47 US government agencies leaked online. The initial product was a web intelligence engine able to better understanding time and historical developments regardless of vertical and the founder, Christopher Ahlberg, had a strong background in analytics, not security. Similarly, there is a new wave of companies, with the idea that security is fundamentally a tech problem, and that strong engineers outside the field will be able to approach security in novel ways. Security is increasingly becoming a data problem, and progress in areas like machine learning mean that the profile of a successful entrepreneur in the space may change in the coming year.
Bridging the gap
As this is an industry where network is key and product development in a longer and less iterative process, a lot needs to be done in bridging the gap between start-up and industry. More so than other sectors.
From an investment perspective, this means that companies will need more funding pre-revenue, whether from public or private sources. From a sales perspective it means it will be more important to know who to speak to within larger organisations and build partnerships that can champion the product and help break through the clutter.
Accelerators like CyLon are a great start. Building a network of industry veterans willing to mentor start-up in the space will help bridge the gap between the security- and the start-up world, and will hopefully be a good launch pad for new technology into a relatively closed off vertical.
Sign up for our newsletter to stay up to date on news from Balderton, and our portfolio.